Infrastructure Hunting Beyond IOCs
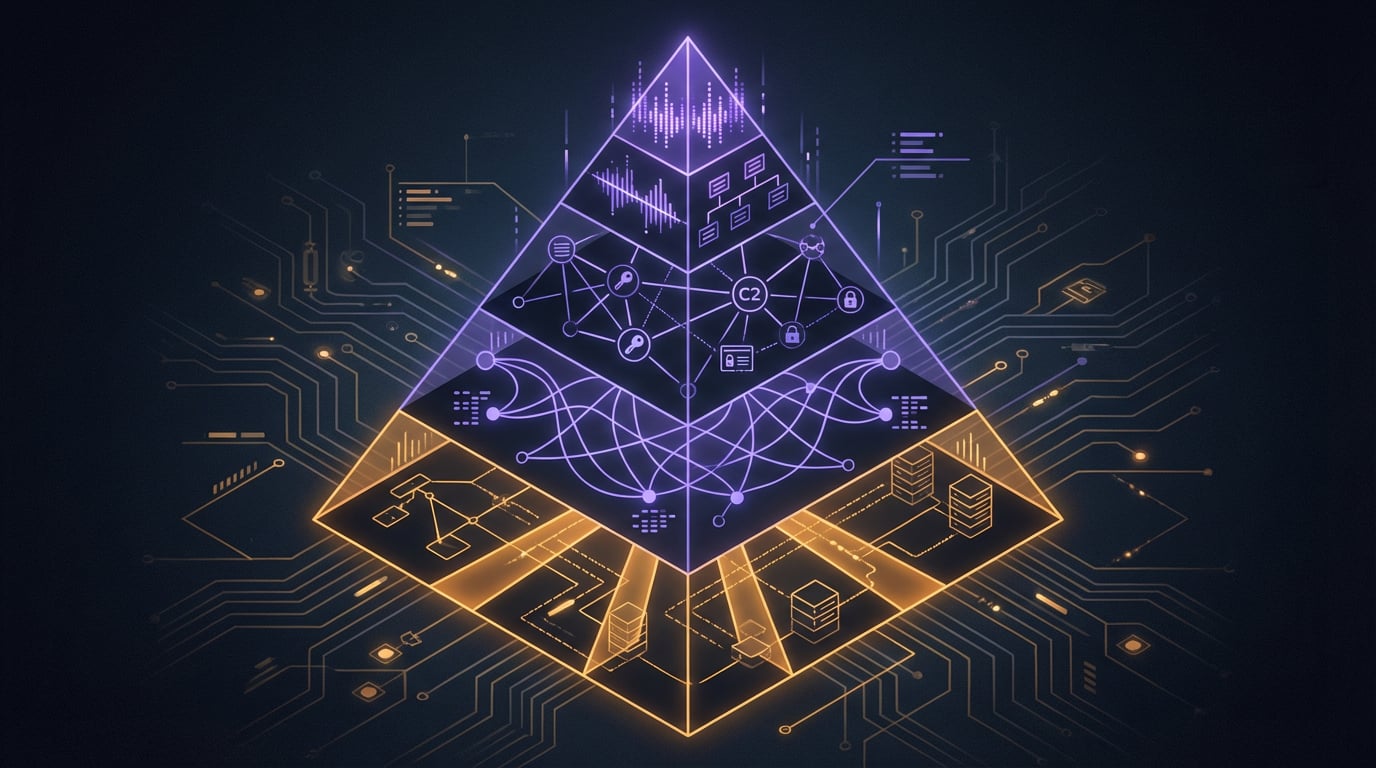
Moving up the Pyramid of Pain — from hash-based detection to hunting adversary infrastructure through behavioral fingerprints and network patterns.
Why Infrastructure Matters
Most threat hunting starts at the bottom of the Pyramid of Pain — hashes, IP addresses, domain names. These are easy to detect but trivial for attackers to change. A ransomware group can recompile their binary and every hash-based detection becomes useless overnight.
Infrastructure sits higher on the pyramid. C2 servers, staging hosts, and distribution nodes take more effort to set up and maintain. If you can identify the patterns an adversary uses to deploy their infrastructure, you can find new instances before they are used in attacks.
Our team started expanding into infrastructure hunting after realizing that file-based detection, while necessary, only catches what has already been used. Finding the infrastructure catches what is being prepared.
The General Approach
The pattern is straightforward: take a known piece of adversary infrastructure, identify what makes it unique, then search for those characteristics at scale using internet scanning platforms.
Every web server has fingerprints — default page content, response headers, port configurations, certificate patterns. Most operators do not bother changing these defaults. That is what makes hunting possible.
Not every match is malicious — verification is always needed — but the hit rate can be surprisingly high when you know what to look for.
Chaining Techniques
Infrastructure hunting is rarely a single step. It is usually a chain: malware analysis gives you indicators, indicators give you infrastructure patterns, patterns give you new infrastructure, and new infrastructure gives you early warning.
Sometimes the pivot starts from YARA rule matches on VirusTotal. Sometimes it starts from a known C2 domain and you work outward. The technique depends on what you have to start with, but the principle is the same — find the pattern, search at scale.
Practical Notes
I built some automation around parts of this workflow — scripts that query scanning platforms, correlate certificates, and flag potential matches based on known fingerprints. The tooling is practical, not fancy. Most of it runs on a schedule and flags anomalies for manual review.
The value is not in the code itself but in knowing what patterns to look for. That knowledge only comes from doing the analysis manually first, understanding how specific threat actors set up their infrastructure, and recognizing the shortcuts they take.
Related Posts
From OSINT to Internal Hunting
How shifting from external OSINT to internal telemetry hunting changed the way I approach threat research — and where most of my published work actually comes from.
What Ransomware Hunting Actually Looks Like
The daily reality of proactive ransomware hunting — from YARA triggers and VirusTotal dashboards to naming new families and building attack chains from telemetry.
Automating Inquiry Triage with AI
How I built a 9-phase AI pipeline to handle threat intelligence inquiries that used to take a week — and what it taught me about building tools from real pain points.
