Production Proactive Hunting
Infrastructure Hunting Toolkit
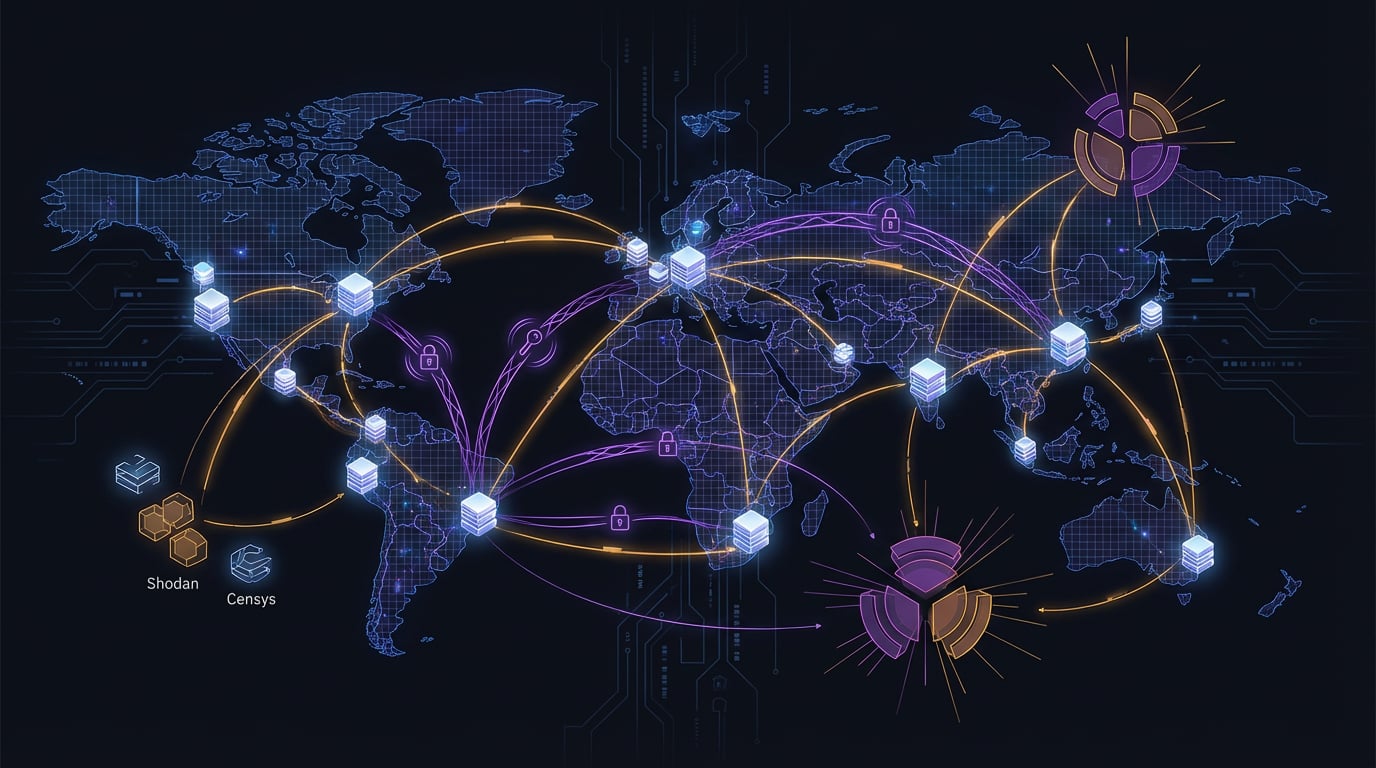
Adversary C2 & Infrastructure Mapping System
Methodology and tooling for adversary infrastructure identification using Shodan, Censys, FOFA, and passive DNS. Maps C2 servers through SSH key pivoting, SSL certificate analysis, HTTP header fingerprinting, ASN attribution, and cloud provider mapping — turning network artifacts into threat actor attribution.
Impact
Identified active C2 infrastructure across multiple campaigns, enabling proactive detection ahead of broader threat activity
Technology Stack
PythonShodan APICensys APIFOFAPassive DNSSSL AnalysisOSINT
