CrazyHunter Campaign Targets Taiwanese Critical Sectors
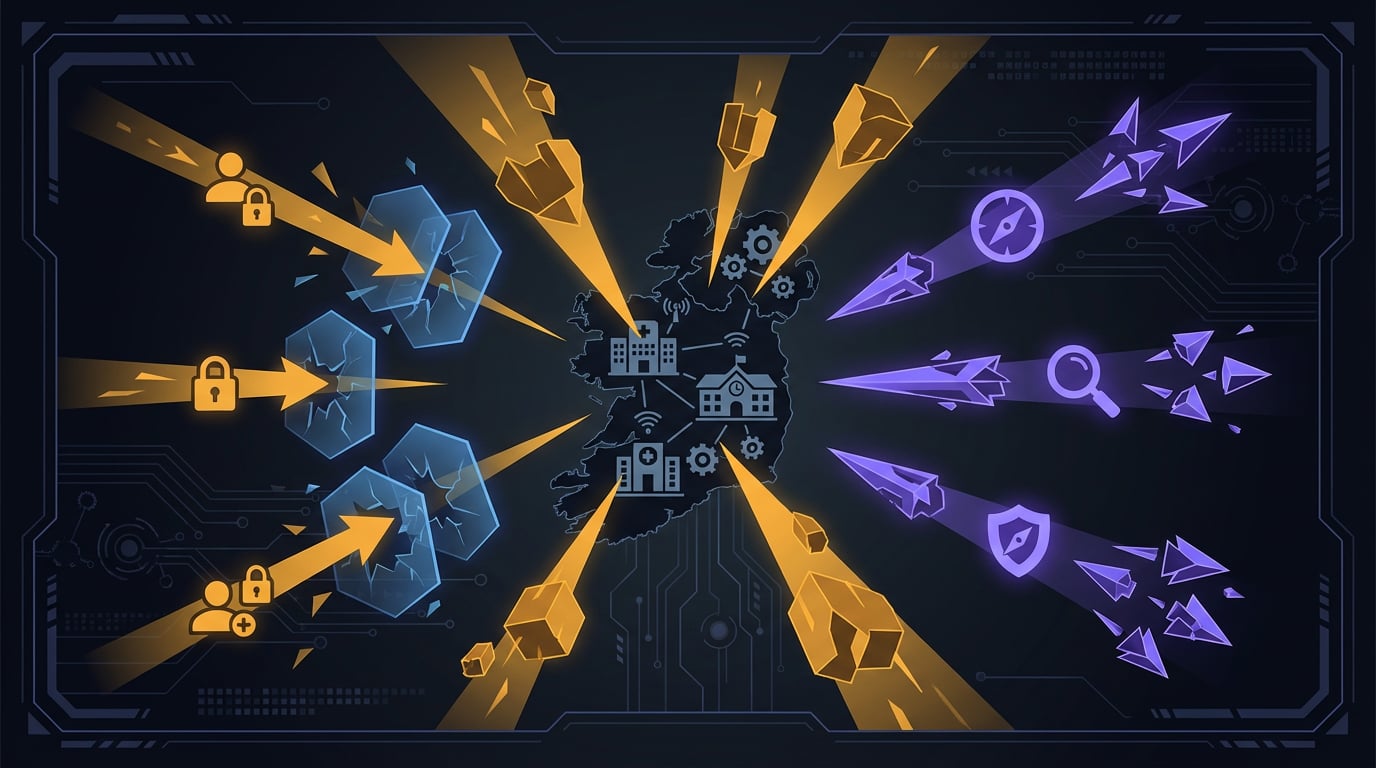
CrazyHunter is a ransomware campaign specifically targeting critical sectors in Taiwan — healthcare institutions and educational organizations. What makes this group notable is their heavy reliance on open-source offensive tools, with approximately 80% of their toolset being publicly available. They employ BYOVD (Bring Your Own Vulnerable Driver) attacks to disable security products, use Prince ransomware as their encryption payload, and leverage tools like SharpGPOAbuse for lateral movement via Group Policy. This article details the full attack chain, victimology analysis, and provides sector-specific mitigation guidance.
Related Research
Unmasking The Gentlemen Ransomware: Tactics, Techniques, and Procedures Revealed
Analysis of a new ransomware group with adaptive defense evasion — custom-patching anti-AV tools mid-attack based on target recon.
Agenda Ransomware Adopts TrueSightKiller for EDR Evasion
Thread detailing how the Agenda ransomware group incorporated the open-source TrueSightKiller tool to disable antivirus and EDR systems via BYOVD techniques.
Web Shells, Tunnels, and Ransomware: Dissecting a Warlock Attack
Deep-dive analysis of Warlock (Water Manaul) ransomware operations revealing new TTPs including persistent BYOVD techniques, TightVNC and Yuze remote access tools, and 15-day dwell time before LockBit-derived ransomware deployment.
Agenda Ransomware Deploys Linux Variant on Windows Systems Through Remote Management Tools and BYOVD Techniques
Discovered Agenda ransomware deploying Linux variants on Windows systems via remote management tools and BYOVD techniques for cross-platform evasion.
